Information Security vs Radioactive Safety
Sat 08 Sep 2012Let us first start with an example of an oversight at the DOE that didn't involve information security.
For this I look to one of my modern day heroes: Phil Broughton AKA Herr Direktor Funranium: radiation safety specialist at UC Berkeley and creator of the Black Blood of the Earth.
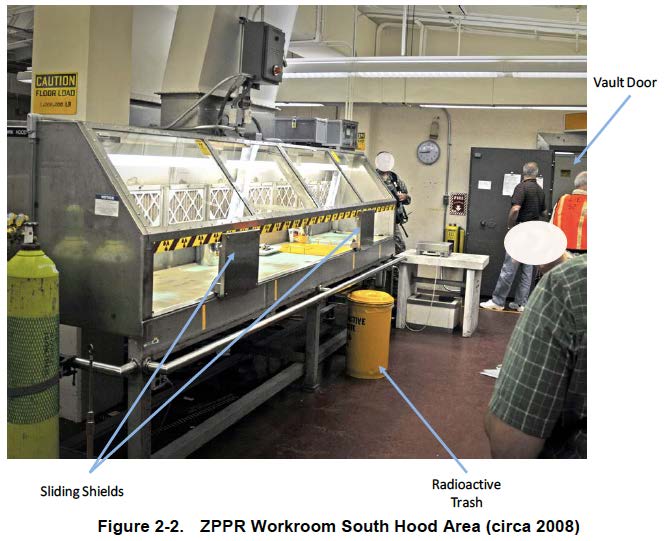
Highlights Magazine: Whats wrong with this picture
YOUR KNOWN INFORMATION:
-
1) You are going to use this setup for handling ZPPR (Zero Power Physics Reactor) nuclear fuel packages with a lot of Pu-240, Am-241 and their resulting fission products, all of which are fairly beefy gamma emitters.
-
2) Gamma dose rates are ~30rad/hr at 10cm from a typical fuel assembly. As a reminder, in the United States, your annual regulatory dose limit is 5rad per year.
-
3) The work operation to be performed involves opening the assemblies to play with the fuel plates within, with the very likely potential for releasing airborne particulates.
-
4) The mass of inhaled Pu-240 alone necessary to make a worker exceed the annual dose limit is ~1 microgram, a quantity that is not visible to the naked eye.
-
5) Herr Direktor Funranium, without a trace of irony, banged his head on the desk, yelling "NO! You have to be shitting me!" when first shown this picture. The good news is that no one died working here. It is otherwise a "No Pants, Bear" grade bad situation. This should give you some idea of how many things are wrong in this picture to pick out.
excerpts from: Funranium Labs
The clouded minds of key decision makers
The root cause for the deficiencies in the above national laboratory boiled down to cost cutting.
I see a parallel between the management of radioactive material and the management of sensitive data throughout the information technology sector.
In both cases you have companies holding material (and/or the waste associated) that carries a great deal of liability surrounding the handling and containment.
It seems quite obvious that one wouldn't leave a vault door open in a room containing radioactive material, or that radioactive trash should be cared for in very specific ways.
The same should be true of your social security number, or credit card numbers, or home address and other personal information. You would expect that your personal information is kept safe, is encrypted, and isn't openly exposed to unauthorized parties.
Yet companies continue to release press statements detailing the mishandling of this data.
We continue to see decision makers viewing security investments as 'insurance policies', as optional recommendations with flexible consequences that are dependant on audit discovery or actual incidents to justify their expense.
A review of recent Information Security failures
Sony
- Impact:
- 77 million accounts exposed with unencrypted personal data.
- 10 Million encrypted Credit Cards exposed.
- Impact:
- 6 million+ customer passwords stolen, passwords hashed, but not salted
Dropbox
- Impact:
- Usernames and passwords stolen from 3d party company, were used for unauthorized access of Dropbox customers' and employee's data.
- Unencrypted customer information exposed and found in an employees email box.
Epsilon
- Impact:
- Exposed names and e-mails of millions of customers stored in more than 108 retail stores plus several huge financial firms like CitiGroup Inc. and the non-profit educational organization, College Board.
RSA Security
- Impact:
- Default encryption keys stolen and used against high profile RSA customers.
- Possibly 40 million employee records stolen.
It's hard to remember the mission when you have to focus on the bottom-line: Let's learn from mistakes
The time has come for companies to acknowledge these oversights. As we move further into the digital age, more and more organizations have the opportunity to interact with millions upon millions of customers with nothing more than a smart phone or a web browser.
-
Liability:
Consider for example, a company with a product that offers free trials along with online purchasing for a product.
Symantec and Ponemon estimate that the cost of a breach can amount to $194 per record.
If that company servers handle an average of 200,000 credit cards per month, thats 278 credit cards per hour. Were a breach to occur on that server, that's a loss of aproximately $54,000.00 per hour.
-
Privacy:
These organizations have a duty to their customers to protect the data that is collected. Not only can personal information be used for identity fraud, the loss of this data (Name, Phone Number, Address, Username, Email , Password) can be used in additional attacks on other companies with whom the customer also does business with.
If you are running an organization that has the potential to bleed $54k an hour due to the mismanagement of security, it is in your best interest to keep those servers and that data under strict lock and key.
This data needs to be protected and accounted for end to end, it needs to be contained and treated with the care you would expect to treat radioactive material. Invariably anything with access to this material becomes contaminated and requires additional resources for care.
A Brave new World
My recommendation is to avoid holding any of this material if possible. Seek secure external means for managing records like these and make sure the vendor you choose has the resources to care for the data.
Indeed, I propose a complete paradigm shift. This legacy model that requires each company to independently ask for your data so that they can separately store it is wasteful and dangerous in the context I've outlined above. Instead, I propose that organizations wishing to identify you, do so through an external site, and only store a unique identifier for you so that they can reference your data when needed.
Authentication can be handled in a similar way. Utilize one of many sources to store 1 password that provides single sign-on for all of your surfing that requires low authorization read-only activity (Reading the news, etc).
For higher authorization activities (commerce, etc), have commerce sites support their own token mechanism, something unique only to that site which requires the pairing of the previously authenticated data.
Duplicating our personal data throughout the Internet on every company's database just makes the attack surface larger. It also makes those organizations spend resources to individually manage all of this data. We have seen what oversights can cost companies who don't have the priorities or resources to properly handle this data.
Imagine if you will, a distribution of systems on the Internet very similar to DNS servers of today (with the modern improvments that learned from the mistakes of DNS). Web-Service servers could establish an encrypted channel and launch a query when a they need your address or phonenumber or email address. The first transaction with a server could leveage an authentication token from you that authorizes the relationship for that paticular web-service. The duration and levels of access to your personal information could be negotiated during this initial encouter, authorizing future interactions. It could even give the consumers greater control over who has access to what information, or at least more so than is given today.
This way, if an commercial entity out there wants to cache or copy this information, they would have to demonstrate that they adhere to the regulations regarding the handling of this data.
Lets move forward with solutions that allow for focused, specialized purposes, interacting together cooperatively rather than a distribution of the same wasteful duplicated data mismanaged from one location to the next.
-Enigma